A new warning for Google Chrome users has emerged, carrying a critical yet straightforward piece of advice: avoid copying and pasting unfamiliar text into your terminal or run dialog box. This advice comes from cybersecurity firm Proofpoint, which has identified a new technique cybercriminals are using to spread malware. The Nature of the Threat Proofpoint […]
Category Archives: Our Blog
Have you ever considered why your smartphone might benefit from a regular reboot? The Federal Bureau of Investigation (FBI) advises a simple yet effective practice: regularly rebooting your phone. This recommendation, backed by cybersecurity experts, plays a crucial role in maintaining your device’s security and integrity. The Importance of Regular Reboots Our smartphones contain a […]
Cybersecurity is a critical aspect of any business, and Las Vegas-based businesses are no exception. The increasing number of cyber threats and attacks on businesses has made it imperative for companies to prioritize cybersecurity. In today’s digital age, businesses are at risk of losing sensitive information, data breaches, and other cyber-attacks, which can be detrimental […]
As many Dallas business owners already know, companies of all sizes and industries can become victims of cyber security attacks. There’s no escaping the need for agile cybersecurity practices, especially in Dallas’s competitive business market. Unfortunately, many small and mid-sized businesses still struggle to preserve their security due to limited resources and a lack of […]
Almost all modern businesses need reliable technology to compete in today’s market – regardless of their size or industry. A well-managed IT infrastructure enables companies to operate more efficiently and deliver a better customer experience. However, IT systems constantly evolve and require a great deal of time and expertise to run smoothly and effectively. […]
No matter their size or industry, all companies need a well-managed, secure IT infrastructure to ensure smooth operations. It enables them to complete daily tasks more efficiently, maintain a competitive edge, and grow over time. However, IT management is a complex process that requires constant upkeep and expert support. It can be challenging for small […]
Microsoft Word users have been relying on third-party plugins and services to check their work for similarity issues. However, the tech giant recently announced that plans are underway to include an in-built plagiarism checker in its Word program. How will this improve your writing experience? The internet has provided a broad range of reference material to […]
Microsoft Edge Vs. Google Chrome Google Chrome is undoubtedly the most popular web browser available on the market. As of June 2020, Chrome boasts a 70 percent market share, while Microsoft Edge is the second most popular option. Microsoft is working tirelessly to boost Edge’s competitiveness in a tight market. The tech giant is looking […]
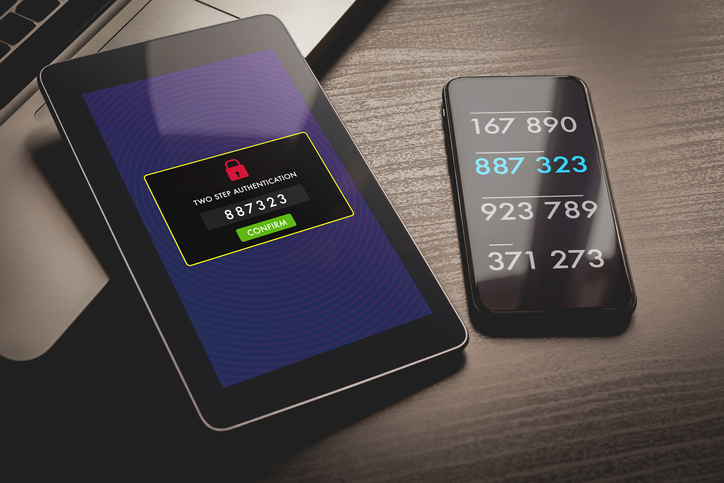
What Is Two-Factor Authentication? When it comes to keeping your business safe from hackers, you’re willing to pull out all the stops. But what if he didn’t have to “pull out all the stops”? What if the only thing you needed was a simple technique for preventing hackers from ever infiltrating your data and networks […]
A Look at the New Apple macOS 11 Big Sur Update The newest macOS update, officially number 11 and called Big Sur, was announced in late June 2020 at the Apple Worldwide Developers Conference (WWDC). Big Sur is such a large and significant update that Apple skipped from version 10.15 straight to 11. For the […]